Inside the Launderer’s Toolkit: How Criminals Clean Dirty Money in 2025

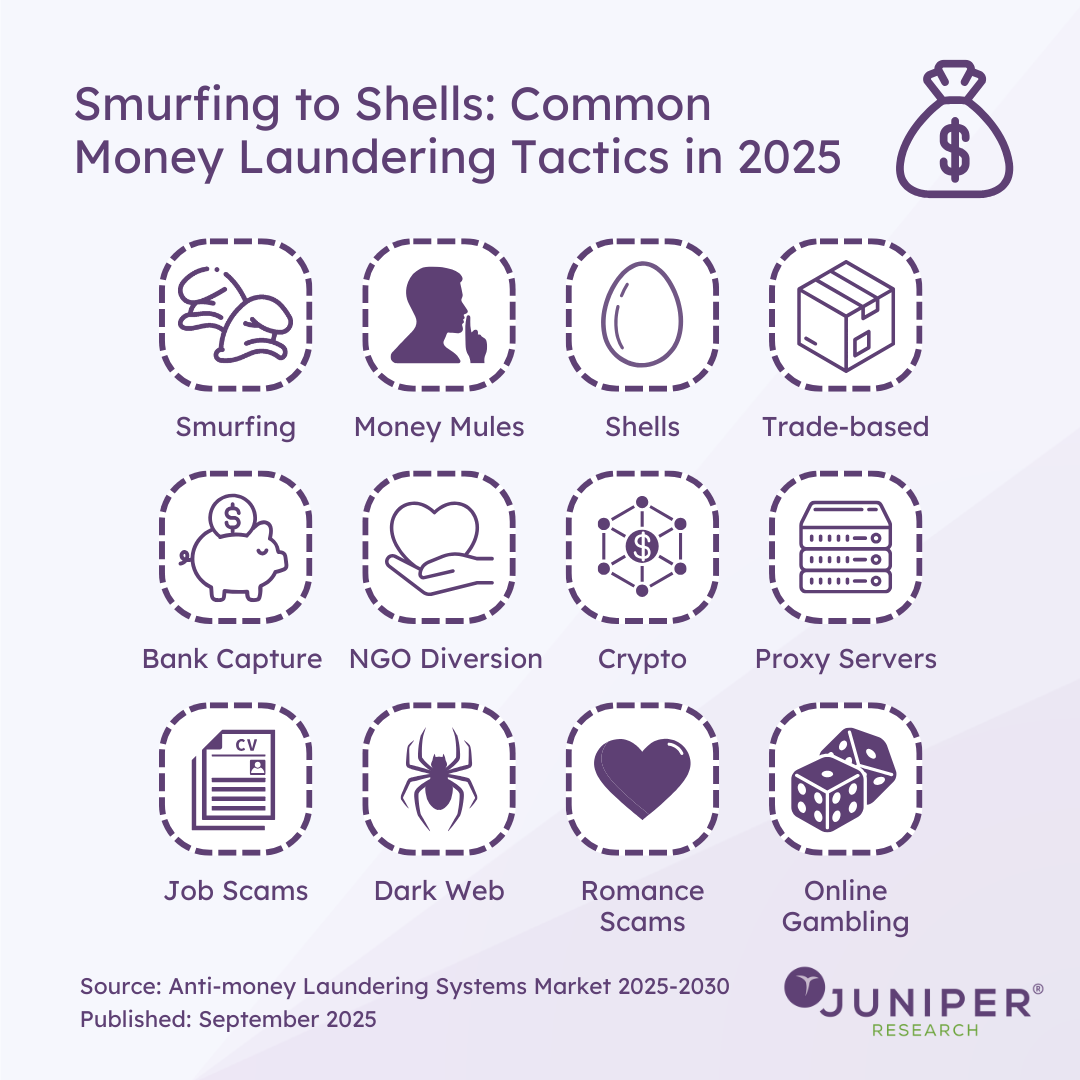
As global regulations tighten and financial systems become more digital, money launderers are evolving their methods to stay one step ahead. Our latest research on the subject has identified 12 tactics most likely to dominate in 2026 — a mix of old-school deception and cutting-edge digital manoeuvres.
Smurfing
Named after the small blue cartoon characters, smurfing involves splitting large sums of money into smaller, seemingly harmless deposits to avoid detection. Rather than one suspicious transaction, criminals scatter hundreds of micro-deposits across multiple accounts. It’s low-tech but surprisingly effective, especially in markets where banks still rely on manual oversight for smaller transfers.
Money Mules
Money mules are the unwitting middlemen of the laundering world. They’re recruited—often through social media or job ads—to transfer money through their accounts, under the pretence of legitimate employment. Some know what they’re doing; many don’t. Either way, the result is the same: dirty money appears to move through a clean individual’s hands.
Shells
Shell companies are hollow corporate entities—businesses that exist on paper but do little or no real trading. They’re perfect for masking ownership and moving funds under the guise of legitimate business activity. From offshore tax havens to complex multi-jurisdictional structures, shells remain one of the most enduring tools for hiding illicit wealth.
Trade-based Laundering
This method dresses financial crime up as global commerce. Criminals manipulate trade invoices—overstating or understating prices, faking shipments, or disguising the nature of goods—to move value across borders. The sheer complexity of international trade makes this a challenge to detect, even for advanced compliance systems.
Bank Capture
In some cases, criminals take the boldest route possible: they capture the bank itself. By infiltrating or outright controlling smaller, poorly regulated financial institutions, they gain direct access to systems that can legitimise illicit funds. Once inside, transactions can be masked, records altered, and oversight quietly neutralised.
NGO Diversion
Non-governmental organisations are built on trust—something money launderers exploit. By routing illegal funds through charities or aid projects, criminals can make their money appear as philanthropic support. In regions affected by conflict or disaster, where financial oversight is limited, this tactic is particularly difficult to uncover.
Crypto
Cryptocurrencies have opened a new frontier for financial crime. Their decentralised, pseudonymous nature allows launderers to move funds quickly across borders without banks or regulators in the way. Sophisticated criminals use mixers and privacy coins to further obscure transaction trails, challenging even the most advanced AML systems.
Proxy Servers
Not all laundering is financial—sometimes it’s digital camouflage. By routing activity through multiple proxy servers or VPNs, criminals can disguise their online identities and locations. This makes it far harder for investigators to connect suspicious financial movements to real-world individuals or organisations.
Job Scams
A new twist on an old con, job scams lure victims with fake employment offers—often in “payment processing” or “financial coordination.” The catch? These workers are actually laundering money for criminals without realising it. Once authorities trace the activity, the “employee” is left carrying the blame.
Dark Web
The dark web remains a thriving ecosystem for illicit trade. From stolen data to illegal substances, everything has a price—and nearly all transactions are in cryptocurrency. Money launderers use dark web markets to mix, move, and disguise their funds, often layering transactions across multiple wallets to throw off digital investigators.
Romance Scams
Few tactics are as emotionally manipulative as romance scams. Fraudsters build online relationships with victims, then invent emergencies or business opportunities to extract money. In some cases, they go further—asking victims to transfer funds on their behalf, turning them into unwitting accomplices in laundering operations.
Online Gambling
Casinos and betting sites—especially unregulated ones—offer the perfect front for laundering. Criminals deposit dirty money as betting funds, place a few strategic wagers, then withdraw their balance as “winnings.” It’s an elegant disguise, with the added benefit of plausible deniability.
As regulators and AML systems adapt, one thing is clear: financial crime is a moving target. Understanding how these tactics work is the first step towards staying ahead of those who aim to exploit the system.
Source: Anti-money Laundering Systems Market 2025-2030
Read the Press Release: AML Systems Market to Surpass $75 Billion by 2030 Globally, With LexisNexis Risk Solutions, Oracle, and Experian Leading the Defence
Download the Whitepaper: From Detection to Prevention: The Next Era of Anti-money Laundering
Latest research, whitepapers & press releases
-
 ReportJune 2026Telecoms & ConnectivityDirect to Cell Market: 2026-2031
ReportJune 2026Telecoms & ConnectivityDirect to Cell Market: 2026-2031Our newest Direct-to-Cell research provides market stakeholders, such as mobile network operators and satellite network operators, with key analysis of the future of this rapidly emerging market.
VIEW -
 ReportMay 2026Telecoms & Connectivity6G Market: 2026-2035
ReportMay 2026Telecoms & Connectivity6G Market: 2026-2035Juniper Research’s 6G Market research suite provides detailed analysis and strategic recommendations for mobile network operators developing their 6G roadmaps in the build up to its standardisation and launch.
VIEW -
 ReportMay 2026Fintech & PaymentsDigital Identity Verification Market: 2026-2030
ReportMay 2026Fintech & PaymentsDigital Identity Verification Market: 2026-2030Our Digital Identity Verification research suite provides detailed analysis of this rapidly changing market; allowing digital identity verification solution providers, financial institutions, and other stakeholders to gain an understanding of key trends and growth opportunities.
VIEW -
 ReportApril 2026Fintech & PaymentsStablecoins Market: 2026-2035
ReportApril 2026Fintech & PaymentsStablecoins Market: 2026-2035Our Stablecoins market research suite provides detailed and insightful analysis of this evolving market; enabling stakeholders such as central banks, commercial banks, stablecoin issuers, and payment service providers to understand future growth, key trends, and the competitive environment.
VIEW -
 ReportApril 2026IoT & Emerging TechnologyPhysical AI in Manufacturing & Logistics Market: 2026-2030
ReportApril 2026IoT & Emerging TechnologyPhysical AI in Manufacturing & Logistics Market: 2026-2030Our Physical AI in Manufacturing and Logistics research suite provides in-depth analysis of the key economic, operational, and technological factors driving growth in this fast-growing market.
VIEW -
 ReportApril 2026Fintech & PaymentsAgentic Commerce Market: 2026-2031
ReportApril 2026Fintech & PaymentsAgentic Commerce Market: 2026-2031Juniper Research’s Agentic Commerce research suite provides an insightful analysis of this rapidly emerging market; enabling stakeholders, including AI developers, payment infrastructure providers, eCommerce marketplaces, merchants and many others, to understand future growth, key trends, and the competitive environment.
VIEW
-
 WhitepaperJune 2026Telecoms & Connectivity
WhitepaperJune 2026Telecoms & ConnectivityNo Tower? No Problem: How Direct to Cell is Rewriting the Rules of Connectivity
Our complimentary whitepaper explores consumer demand for direct to cell services and provides strategic recommendations for how MNOs can optimise these services.
VIEW -
 WhitepaperMay 2026Telecoms & Connectivity
WhitepaperMay 2026Telecoms & ConnectivityLearning from 5G - How MNOs Can Make 6G a Success
Our complimentary whitepaper, Learning from 5G - How MNOs Can Make 6G a Success, explores the lessons that mobile network operators can learn from the development and commercialisation of 5G and apply to 6G.
VIEW -
 WhitepaperMay 2026Fintech & Payments
WhitepaperMay 2026Fintech & PaymentsDigital Identity Verification in an Era of AI, Fraud & Regulatory Change
This complimentary whitepaper examines the state of the digital identity verification market: considering the impact of regulatory developments, emerging risk tactics, and how identity verification is evolving beyond traditional customer and merchant onboarding.
VIEW -
 WhitepaperApril 2026Fintech & Payments
WhitepaperApril 2026Fintech & PaymentsPayment Rails Without Borders: The Rise of Stablecoins
Our complimentary whitepaper, Payment Rails Without Borders: The Rise of Stablecoins, analyses the history of stablecoin from its inception to the current day. It also provides insight into key trends shaping the stablecoin market, and an evaluation of stablecoins versus traditional payment rails.
VIEW -
 WhitepaperApril 2026IoT & Emerging Technology
WhitepaperApril 2026IoT & Emerging TechnologyKey Growth Opportunities for Physical AI in 2026
Our complimentary whitepaper, Key Growth Opportunities for Physical AI in 2026, provides insight into the rapidly evolving physical AI in manufacturing and logistics market; highlighting the countries in which high demand for automation in these industries is anticipated over the next five years.
VIEW -
 WhitepaperApril 2026Fintech & Payments
WhitepaperApril 2026Fintech & PaymentsAgentic Commerce - Revolution or False Dawn?
Our complimentary whitepaper assesses the trends that are increasing agentic commerce adoption, and challenges to agentic commerce usage. Additionally, it includes a forecast summary of the global spend on agentic commerce by 2030.
VIEW
-
Telecoms & Connectivity
Direct to Cell: Monthly Active Users to Reach Over 130 Million by 2031, But Usage Forecast to Be Lower Than Anticipated
June 2026 -
Fintech & Payments
Merchant Payments: a $100 Trillion Opportunity for Providers, but Global Complexity & Friendly Fraud Creates Challenges
May 2026 -
Fintech & Payments
Calling All Digital Identity & Cybersecurity Innovators: Future Digital Awards Now Open for 2026
May 2026 -
Telecoms & Connectivity
Juniper Research Predicts the US and South Korea Will Lead 6G Launches in 2029
May 2026 -
Fintech & Payments
Cross-border Payment Transactions to Hit $63 Trillion by 2030 Globally, as Cross-border eCommerce Scales Rapidly
May 2026 -
Fintech & Payments
Corporate Cards: 66 Million Cards in Use Globally by 2030, with Adoption Rising Among Microbusinesses
May 2026